FortiPAM
Protect critical assets and manage privileged accounts with FortiPAM
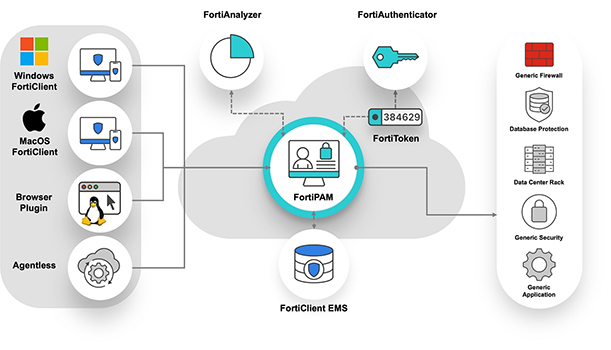
FortiPAM provides privileged access management, control, and monitoring of elevated and privileged accounts, processes, and critical systems across the entire IT environment. FortiPAM is part of the Fortinet Security Fabric, integrating with products such as FortiClient, FortiAuthenticator, and FortiToken.
Features and Benefits
FortiGate NGFW is the world’s most deployed network firewall, delivering unparalleled AI-powered security performance and threat intelligence, along with full visibility and secure networking convergence.
- Manage Privileged Accounts - Easily keep all account credentials secure and automatically change passwords
- Control Privileged User Access - Role-based access controls through centrally managed administrative policies
- Monitor Privileged Activity - Get full video recording and keystroke monitoring of privileged-resource access for auditing.
- Get Zero-Trust for Privileged Resources - Apply ZTNA controls to users and devices for enhanced security when accessing privileged resources
- Secure Privileged Account Information - Ensure that no sensitive privileged account information is delivered to the end-user’s device.
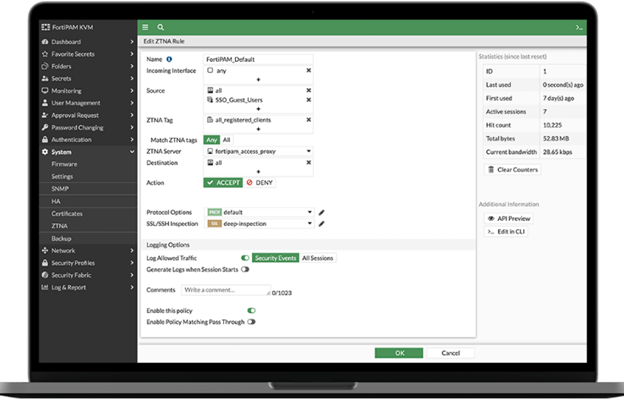
ZTNA Controls for Critical Access
Critical assets need to be protected with the highest level of security. FortiPAM allows for enhanced security including zero-trust network access (ZTNA) controls when users try to access critical assets.
ZTNA tags can be applied to check device posture for vulnerabilities, installed AV, location, and more. These checks are done continuously so if something changes on the device, it can be disconnected from the critical asset. In this way, FortiPAM ensures that the users and devices accessing critical assets are secure and prevents threats from impacting the asset.
Strong Security for Privileged Accounts
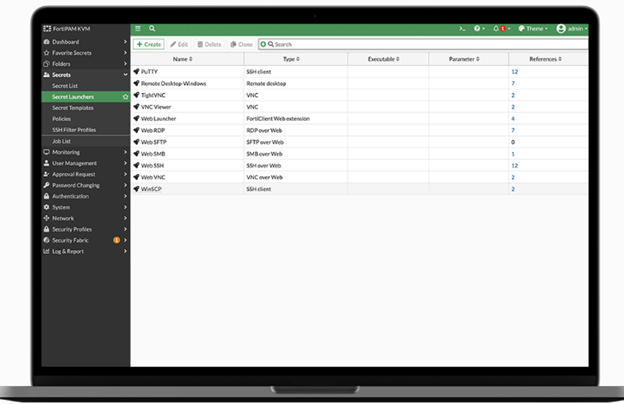
You can use pre-built application- or web-based launchers, or easily create your own launch templates to provide secure access for your organization's most critical resources.
Once launchers for privileged resources have been created, they can be opened by users that have been granted access to them. When launched, all actions within the resource will be monitored and recorded for auditing purposes, with ability to terminate sessions. In addition, based on policy, passwords for the resources can be changed on a scheduled basis or when the resource is checked in by the user.